
Cyberoam CR35iNG
Future-ready Security for SOHO/ROBO networks
Cyberoam – a Sophos Company, secures organizations with its wide range of product offerings at the network gateway. For the latest Cyberoam products, please visit our Sophos's store EnterpriseAV.com

Sorry, this product is no longer available, please contact us for a replacement.
Overview:
Cyberoam NG series of Unified Threat Management appliances are the Next-Generation network security appliances that include UTM security features and performance required for future networks. The NG series for SOHO offer “the fastest UTMs made for SMBs” to small offices. The best-in-class hardware along with software to match, enables the NG series to offer unmatched throughput speeds, compared to any other UTM appliance in this market segment. This assures support for future IT trends in organizations like high-speed Internet and rising number of devices in organizations – offering future-ready security for small office networks.
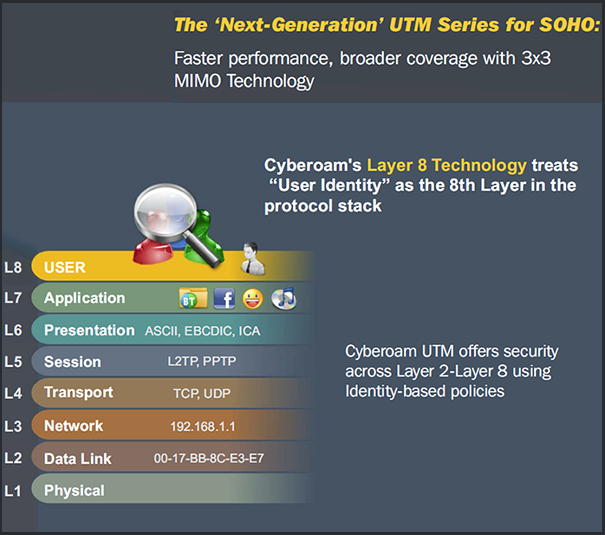
With Cyberoam NG series, businesses get assured Security, Connectivity and Productivity. The Layer 8 Technology treats User-Identity as the 8th Layer or the HUMAN layer in the protocol stack. It attaches User-Identity to security, which adds speed to an organization’s security by offering instant visibility into the source of attacks by username rather than only IP address. Cyberoam’s Extensible Security Architecture (ESA) supports feature enhancements that can be developed rapidly and deployed with minimum efforts, offering future-ready security to organizations.
| Cyberoam UTM features assure Security, Connectivity, Productivity | ||
|---|---|---|
|
|
|
Hardware UTM Appliances for Small & Branch Offices:
Cyberoam UTM appliances deliver unified security over a single console, enabling small offices to shift from plain firewalls to comprehensive UTM protection with cost-effective, yet powerful security against malware, spam, Trojans, DoS, DDoS, phishing, pharming and intrusions. At the same time, large organizations can implement uniform security and gain high visibility into remote and branch offices with centralized management and Layer 8 Identity-based security. These offices also gain secure remote access, redundant WAN connectivity and availability, data leakage protection and advanced networking features.
Product Features
| CR15wiNG | CR25wiNG | CR35wiNG | CR15iNG | CR25iNG | CR35iNG | |
|---|---|---|---|---|---|---|
| Hardware Specifications | ||||||
| Copper GbE Ports | 3 | 4 | 6 | 3 | 4 | 6 |
| Console Ports (RJ45) | 1 | 1 | 1 | 1 | 1 | 1 |
| USB Ports | 2 | 2 | 2 | 2 | 2 | 2 |
| Hardware Bypass Segments# | - | - | - | - | - | - |
| Configurable Internal/DMZ/WAN Ports | Yes | Yes | Yes | Yes | Yes | Yes |
| System Performance* | ||||||
| Firewall Throughput (UDP) (Mbps) | 1,000 | 1,500 | 2.300 | 1,000 | 1,500 | 2,300 |
| Firewall Throughput (TCP) (Mbps) | 750 | 1,000 | 2,000 | 750 | 1,000 | 2,000 |
| New sessions/second | 3,500 | 5,000 | 12,000 | 3,500 | 5,000 | 12,000 |
| Concurrent sessions | 60,000 | 150,000 | 350,000 | 60,000 | 150,000 | 350,000 |
| IPSec VPN Throughput (Mbps) | 110 | 210 | 250 | 110 | 210 | 250 |
| No. of IPSec Tunnels | 50 | 100 | 150 | 50 | 100 | 150 |
| SSL VPN Throughput (Mbps) | 50 | 75 | 100 | 50 | 75 | 100 |
| WAF Protected Throughput (Mbps) | -NA- | 45 | 65 | -NA- | 45 | 65 |
| Anti-Virus Throughput (Mbps) | 180 | 300 | 525 | 180 | 300 | 525 |
| IPS Throughput (Mbps) | 140 | 200 | 350 | 140 | 200 | 350 |
| UTM Throughput (Mbps) | 80 | 110 | 210 | 80 | 110 | 210 |
| Authenticated Users/Nodes | Unlimited | Unlimited | Unlimited | Unlimited | Unlimited | Unlimited |
# If Enabled, will bypass traffic only in case of Power failure.
* Antivirus, IPS and UTM performance is measured based on HTTP traffic as per RFC 3511 guidelines. Actual performance may vary depending on the real network traffic environments.
| Key Features | |
|---|---|
| Layer 8 Identity-based policies | Role-based access at remote locations |
| Visibility into who is doing what | |
| Comprehensive UTM Security | Stateful Inspection Firewall |
| Intrusion Prevention System | |
| Anti-Virus & Anti-Spyware | |
| Anti-Spam | |
| Web Filtering | |
| Application Visibility & Control | |
| On-appliance Reporting | |
| Web Application Firewall | |
| Outbound Spam Protection | |
| Secure Remote Access | IPSec VPN |
| L2TP | |
| PPTP | |
| SSL VPN | |
| WAN Connectivity & Availability | Bandwidth Management |
| Multiple Link Management | |
| 3G / WiMAx Support | |
| Advanced Networking | Multi-core Processing |
| Extensible Security Architecture | |
| Active-Active High Availability | |
| IPv6 Ready Gold Certified | |
| Wi-Fi Security | Wireless Standards IEEE 802.11 n/b/g (WEP, WPA, WPA2, 802.11i, TKIP, AES, PSK, 802.1x EAP) |
| Up to 8 bssid Access Points | |
| Centralized Security Management | CCC Appliances |
| Cyberoam iView Open Source Solution – Logging & Reporting | |
| Cyberoam iView Appliances – Logging & Reporting | |
Specifications:
| Specification | ||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
Interfaces
System Performance*
Stateful Inspection Firewall - Layer 8 (User - Identity) Firewall GatewayAnti-Virus & Anti-Spyware -Virus,Worm,Trojan: Detection &Removal Gateway Anti-Spam - Inbound/Outbound Scanning Intrusion Prevention System - Signatures: Default (4500+), Custom Web Filtering - InbuiltWeb Category Database Application Filtering - Inbuilt Application Category Database - P2Papplications e.g. Skype- Layer 7 (Applications) & Layer 8 (User - Identity) Visibility |
Web Application Firewall - Positive Protection model Virtual Private Network - IPSec, L2TP, PPTP SSL VPN -TCP&UDPTunneling Instant Messaging (IM) Management -Yahoo and Windows Live Messenger WirelessWAN -USBport 3G/4G and Wimax Support Bandwidth Management - Application and User Identity based Bandwidth User Identity and Group Based Controls -Access time restriction Networking - Failover - Automated Failover/Failback, Multi-WAN High Availability - Active-Active |
Administration & System Management -Web-based configuration wizard User Authentication - Internal database Logging/Monitoring - Graphical real-time and historical monitoring On-Appliance Cyberoam-iView Reporting - IntegratedWeb-based Reporting tool - IPSecVPNClient** - Inter-operability with major IPSecVPNGateways Certification - ICSAFirewall - Corporate
Compliance -CE
Power
Environmental
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||
| Concurrent VPN Sessions for Cyberoam UTM Appliances | |||
|---|---|---|---|
| Cyberoam Model | IPSec VPN Tunnels | IPSec Remote Access Users | SSL VPN Tunnels |
| Cyberoam NG Series of Appliances | |||
| CR15iNG/CR15wiNG | 50 | 15 | 30 |
| CR25iNG/CR25wiNG | 100 | 25 | 50 |
| CR35iNG/CR35wiNG | 150 | 35 | 75 |
| CR50iNG | 200 | 50 | 100 |
| CR100iNG | 250 | 100 | 200 |
| CR200iNG | 300 | 200 | 300 |
| CR300iNG | 400 | 300 | 400 |
| CR2500iNG | 3,000 | 2,500 | 3,000 |
| Cyberoam i, ia, wi Series of Appliances | |||
| CR15i/CR15wi | 22 | 15 | Not Applicable |
| CR25ia/CR25wi | 37 | 25 | 25 |
| CR35ia/CR35wi | 52 | 35 | 35 |
| CR50ia | 75 | 50 | 50 |
| CR100ia | 150 | 100 | 100 |
| CR200i | 300 | 200 | 200 |
| CR300i | 450 | 300 | 300 |
| CR500ia | 800 | 500 | 550 |
| CR750ia | 900 | 750 | 750 |
| CR1000ia | 1,500 | 1,000 | 1,000 |
| CR1500ia | 2,250 | 1,500 | 1,500 |
*Antivirus, IPS and UTM performance is measured based on HTTP traffic as per RFC 3511 guidelines. Actual performance may vary depending on the real network traffic environments.
**Additional Purchase Required. Inbound and Outbound Spam filtering cannot be used simultaneously.
Supports and Subscriptions:
Subscriptions:
- Antivirus and Anti Spam Subscription: Protection against Internet and mail based malware
- Comprehensive Value Subscription: Comprehensive Value Subscription includes Anti Malware, Anti Spam, Web and Application Filter, WAF, Intrusion Prevention System , 24x7 Support, hardware warranty and RMA fulfillment
- Gateway Anti Spam: Zero-hour protection with industry’s highest spam detection capabilities
- Gateway Anti Virus: Gateway level protection from viruses, worms and malicious code
- Intrusion Prevention System: Protects from intrusion attempts, DoS attacks, malicious code transmission, backdoor activity and blended threats
- Outbound Anti Spam: Protects service providers from recurring incidents of outbound spam in the network.
- Security Value Subscription Plus: Cyberoam Security Value Subscription Plus includes Anti Malware, Web and Application Filter, Intrusion Prevention System , 24x7 Support, hardware warranty and RMA fulfillment
- Security Value Subscription: Cyberoam Security Value Subscription includes Anti Malware, Web and Application Filter and Intrusion Prevention System, 8x5 Support, hardware warranty and RMA fulfillment
- Total Value Subscription Plus: Cyberoam Total Value Subscription Plus includes Anti Malware, Anti Spam, Web and Application Filter, Intrusion Prevention System, 24x7 Support, hardware warranty and RMA fulfillment
- Total Value Subscription: Cyberoam Total Value Subscription includes Anti Malware, Anti Spam, Web and Application Filter and Intrusion Prevention System, 8x5 Support, hardware warranty and RMA fulfillment
- Web and Application Filter: Dependable web and application filtering to control and report non-work and malicious web and network traffic activity.
- Web Application Firewall: Prevents exploitation of web applications vulnerabilities.
Supports
Basic 8x5 Support: 8x5 Phone, Email and Web Chat support with firmware upgrades , hardware warranty and RMA fulfillment
Premium Support 24x7: 24x7 Phone, Email and Web Chat support with firmware upgrades, hardware warranty and RMA fulfillment
| 8x5 Basic Support | 24x7 Premium Support | |
|---|---|---|
| Technical Support | ||
| Timings | 10AM - 6PM (Local Time Zone) | Anytime during the day |
| Web Based Support | Yes | Yes |
| Phone Based Support | Yes | Yes |
| Chat Based Support | Yes | Yes |
| Number of support incidents per annual subscription | Unlimited | Unlimited |
| First Response Time | 4 Hours | 1 Hour |
| Onsite Support Services* | - | Fee Based Service |
| Software Support | ||
| Software & OS Upgrades and Patches | Yes | Yes |
| Hot Fixes and Enhancement upgrades | Yes | Yes |
| Signature & database update | Yes | Yes |
| Hardware Warranty | ||
| Limited Hardware warranty & Replacement | Yes | Yes |
| Return and Replacement policy | 10 Days | 4 Days |
| Advanced Hardware Replacement | - | Yes |
| Customer Portal | ||
| Product Documentation and Guides | Yes | Yes |
| Technical Trainings - CCNSP & CCNSE Certifications | Fee Based | Fee Based |
| Online Demo | Yes | Yes |
| Version Release Notes | Yes | Yes |
| Support Renewals | ||
| One, two and three (1, 2 and 3) Year Renewals | Yes | Yes |
Download the Cyberoam Basic Support Plan Datasheet (PDF).
Download the Cyberoam Premium Support Plan Datasheet (PDF).
Documentation:
Download the Cyberoam CR35iNG Datasheet (PDF).
Download the Cyberoam UTM Techsheet (PDF).
