 Cyberoam SSL VPN Appliances Overview
Cyberoam SSL VPN Appliances Overview
Comprehensive Internet Security Systems
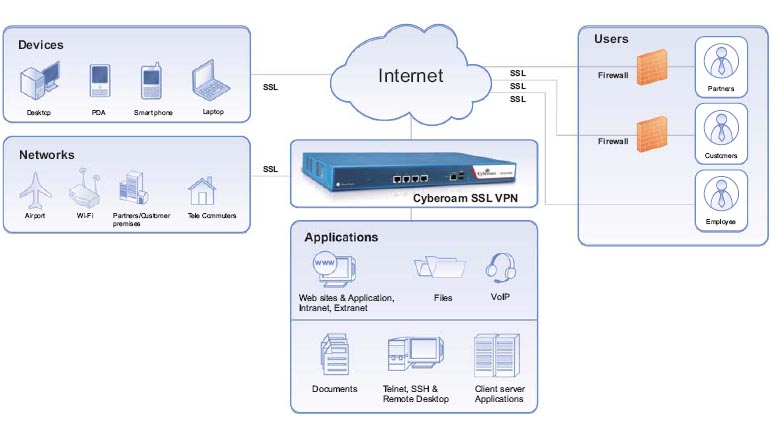
Cyberoam’s SSL VPN appliances offer breakthrough technology in high performance, secure remote access to the corporate network. With Cyberoam SSL VPN, enterprises can provide secure connectivity to critical data and applications on their central network to road warriors, branch offices, telecommuters as well as guest users and partners.
Cyberoam SSL VPN appliances deliver high performance in addition to strong end-point security and granular access control to enterprises, helping them remain compliant with regulatory requirements. Identity-based logs of network access enable organizations to securely extend their networks with complete knowledge who is remotely accessing what in their network. With client-less configuration, they offer high ROI, high performance secure remote access to small, medium and large enterprises.
Key Benefits:
- High performance
- End-point security
- Policy-based resource access control
- Zero-client administration
- High ROI
Return on Investment
By eliminating complex client configurations and providing seamless connectivity to employees, Cyberoam SSL VPN appliances minimize connection setup time and cost. By delivering anytime, anywhere high performance remote access to employees and partners, they reduce the cost of doing business and help to deliver high ROI and rapid access. Further, granular access controls lower the risks and costs involved in securing remote access, thereby increasing the security ROI.
Ease of Use
The third-generation Cyberoam SSL VPN appliances support the most popular enterprise platforms – Windows®, Mac OS and Linux® - ensuring that no user is left behind. Deployment in existing networks is facilitated by support of existing authentication solutions. Rather than granting conventional full network access to remote users, four modes of access provide as much, or as little, access as needed - all with minimal yet central configuration.
Automatic re-connection between user and gateways and high availability clustering ensure continuous connectivity to critical applications and data.

